Roger Clarke's Web-Site
© Xamax Consultancy Pty Ltd, 1995-2024

Infrastructure
& Privacy
Matilda
Roger Clarke's Web-Site© Xamax Consultancy Pty Ltd, 1995-2024 |

|
|||||
| HOME | eBusiness |
Information Infrastructure |
Dataveillance & Privacy |
Identity Matters | Other Topics | |
| What's New |
Waltzing Matilda | Advanced Site-Search | ||||
Version of 26 July 2011, revs. Aug 2011, Aug 2012, Sep 2017
© Xamax Consultancy Pty Ltd, 2011-17
Available under an AEShareNet ![]() licence or a Creative
Commons
licence or a Creative
Commons  licence.
licence.
This document is at http://www.rogerclarke.com/II/Passwords.html
If all you want is a quick guide to how to create a password, here's a recently revised version of mainstream thinking:
Cranor L.F. et al. (2017) 'Choose better passwords with the help of science' The Conversation, 30 Aug 2017, at https://theconversation.com/choose-better-passwords-with-the-help-of-science-82361
People often ask questions about passwords, and I've always been surprised how hard it is to point to decent sources of advice. This document provides a short statement of the things I think people ought to know. The sections are:
Feel free to email me suggestions for improvement, and questions that I've failed to answer.
A password is a string of characters that is input by a person to a computer service, so that the service can check whether the person should be allowed access.
Computer services want to limit access to some data and to some of their software.
And people want to prevent access to their data by other people who they haven't authorised.
When a person registers for an account with a computer service, they are assigned a 'username' (or 'login-id'), and are either assigned a password to go with the username, or asked to nominate their own password.
Each time that the user asks for access to the account, they do so by providing their username and password.
The computer service checks whether the password is the right one for that username.
A password only achieves its aim of protecting data and software if it's a secret shared with no-one else, i.e. it needs to be something that only the relevant person knows.
Passwords are used to protect valuable assets. Because those assets are attractive, people will be interested in gaining access to them. So some people will look for opportunities to acquire passwords. And some people will actively work at acquiring passwords, in what is usually called a 'password attack'.
A discussion of risks to passwords is provided in a later section. The fundamental issue is that a password offers some security, but it's easily 'compromised', i.e. discovered by someone else.
A good password is usually referred to as being 'strong'. Some guidance on the creation of strong passwords is provided in a later section. But briefly, a password is more secure if it's hard to guess, i.e. long and not obvious; but the longer and less obvious the password is, the more likely that you'll forget it.
So, when you choose a password, balance security against practicality. The more harm that people can do to you if they gain access to an account, the more care you should take in creating and protecting the password.
Remembering even one password is bad enough, but remembering a lot of passwords is even more challenging, especially for the accounts that you use infrequently. My daughter quickly counted over 20 - Internet banking, credit-card, debit-card; personal email (3), home network; workplace email, workplace intranets (2), workplace purchasing, job-related sites (3); social networking (3); online merchants (5).
It's not so bad to use a common, easy-to-remember password for multiple unimportant accounts. But, for each of your important accounts, use a special password for that account only; and avoid recording it, i.e. store a reminder rather than the password itself.
This section lists some of the key things that can go wrong, and identifies some safeguards you can use. I've used 'avoid' for bad practices, and positive expressions for better practices.
Someone may try something obvious and get lucky. Or they may try a common default password (which was how Murdoch's 'News of the World' broke into phone-message banks).
Avoid an obvious word, or obvious data that's associated with you (e.g. your birthdate, your name, a close relative's name).
If the account is issued with a default password, only use that password once, to gain access the first time, and then immediately change it.
Programs exist that discover passwords by testing large numbers of combinations of characters. They are typically based on a list called a 'dictionary' (although it contains a lot more than just normal words).
Avoid simple words and examples of passwords that have been published.
Use the available guidance in creating a strong password.
Someone may see the display of what you key in, or which keys you hit, possibly directly, or with the aid of a nearby camera or CCTV.
Avoid keying your password into a field that displays in clear on the screen.
Avoid keying your password when someone is watching your hands. (This applies especially to your flatmates, family-members and workmates).
Use more than one finger, and preferably both hands, to confuse any observer.
Obscure the keys you strike by putting your hands or body in the way.
Change your password very shortly after it may have been observed, e.g. when you've used it in an Internet cafe or airport lounge.
The term 'key-logger' refers to malware that can detect what you key in.
Install, maintain and run 'brand-name' anti-malware software. You need to be confident in that software, so don't accept dodgy-looking offers.
When in a relatively secure environment (hopefully this includes at home), prefer a mouse-based user-interface (where you click on the relevant characters on the screen, rather than typing them on the keyboard). But this is insecure in a public space like an Internet cafe.
Someone or something in the network may see the password as it goes by.
Avoid providing a password unless you're on an encrypted link
(e.g.
one that uses SSL/TLS - which displays 'https' in your web-browser).
Avoid sending your password in an unencrypted email-message, or make sure the password and information about the account it's used for are not in the same email.
Someone may trick you into providing your password to them.
Avoid clicking on a hotlink in an email and then entering your password.
Avoid keying in your password unless you are confident you are communicating with the right server, e.g. you've typed the URL from a reliable source, or you're using a bookmark that you previously typed in.
Avoid keying your password into a web-site that offers to check the strength of your password unless you're confident that the site is reliable.
Avoid using the same password for more than one account.
OR
Avoid using the same password for more than one important account.
It's less risky to use one password for the myriad accounts that you're forced to have but where the harm would be minimal even if it's compromised (e.g. commentators' accounts, e-mailing list admin accounts, subscriptions to paid content, reviewers' accounts).
Someone or something snooping around your machine may find your password.
Ideally, avoid recording your passwords. (But that's difficult advice to follow!).
Avoid recording your passwords, but instead record reminders to help you remember what your passwords are.
Avoid recording all of your passwords or reminders in one place.
Obscure the fact that they are passwords or password reminders, but avoid relying on this as your only protection.
Obscure your records of passwords or reminders by encrypting them (using cryptographic software together with a crypto-key and/or 'master' password).
Prevent other people from accessing your records of passwords or reminders, e.g. by carrying them on you, whether on paper or in a device that isn't network-connected (e.g. a thumbdrive).
Avoid storing your password-related records on anyone else's device; or, if you do, then make sure that the records are crypto-protected against the organisation that stores it for you, and against others.
Products are available that enable you to keep an encrypted database of usernames and passwords on your own device or thumbdrive (e.g. Password Safe). The weak link is that everything in the database is protected by ... a single password.
It's normal for there to be a way to override the password on an account, and generate a new one. A replacement password has to be re-issued. The usual approach is to send it to the email-account that you nominated when you opened the account, although in some circumstances you may need to present yourself at a counter and bring some evidence of identity with you.
Record the email-address that you use when you open each account.
Make sure that you have access to those accounts, and that no-one else has.
If you have any reason to suspect that someone may have discovered your password, get into a relatively secure environment and then change it.
If you have used any password for a long time (and protection of the account is important), assume that it's been compromised, and change it.
How long is 'a long time'? The more important the account, the more often you should change the password.
There is absolutely no reason why any service-provider should ever store their users' passwords. It's sufficient to use an algorithm to generate a 'one-way hash' of the password, and always 'hash' the passwords that users key in and compare the 'hashes'. So any service-provider that has passwords available for accidental disclosure, or access by staff or hackers, should be sued, and sacked.
If a service-provider you use is technically incompetent or untrustworthy, or you become aware of them being hacked, either move somewhere else or use a unique password for that site alone (so that other accounts you use aren't compromised just because this one is), and change it frequently.
The file of hashed password-values that is used to authenticate passwords may be acquired by someone, commonly by that person breaking into the device on which it's stored.
If the means whereby the hashing is performed is known, or can be interpolated, then a 'brute force attack' can be mounted. This involves generating a table containing the value of the hash of every possible password - or at least of every possible password up to some length, such as 8 or 12 characters. Each hash in the file of hashed passwords can then be compared against the table, thereby discovering the corresponding password.
A great deal of processing power is needed to mount such an attack; but inexpensive processors and multi-processor configurations are now sufficiently fast that attacks are succeeding.
Organisations that store hashed passwords have a choice of hashing algorithms, and at any given time some of them are preferable to others. Organisations can also make the attack much harder, by including a random number in the calculation of each hash - which is commonly referred to as 'salting the password hash'. These has the effect of forcing an attacker to compute very large numbers of tables, i.e. as many tables as there are random numbers used as salts. That substantially defeats this kind of attack.
The salting of hashes has been a well-established technique for many years, and organisations that don't use it are guilty of seriously inadequate security practices; but there are many such organisations, and at this stage their culpability is not subject to legal sanctions.
The only real defence that an individual has against the combined threat of this attack and incompetent security practices by organisations, is to use long passphrases. Again, it is highly inadvisable to use the same password on more than one account that is important to you, because if any one of your accounts is exposed in this manner, the attacker has the password to all of your accounts that use that password.
A password needs to be long enough to make it difficult for a machine to guess, and for an observer to remember.
But a password also needs to be short enough to remember.
Most service providers require at least 6, perhaps 8 characters. Most allow at least 10. Many allow quite long passwords (often called pass-phrases).
Most systems are 'case-sensitive'. i.e. capitals (upper case letters like 'X') and lower-case letters (like 'x') are treated differently. Many systems support large numbers of 'special characters' (many of them punctuation marks) and treat the space-bar as a separate character. So you may be able to use any combination of capitals, lower-case, digits, spaces and any punctuation mark you can find on each of the keyboards you use.
Here are some ways to create reasonably secure passwords that you can remember, with examples of each.
Do not use any of the examples below! They're published, so they've probably already been added to the 'dictionaries' that attackers use to break in to accounts.
Use a word or phrase, but vary it in a way that you'll
remember
e.g. counterweight becomes counterwait
Reminder: what
I do at the Post Office
But this may still be very weak, so use something
else below as well
Use a word or phrase, but substitute some
characters
However this is subject to a 'dictionary attack', so add
extra characters
Blondie becomes Bl0nd1e!! (i.e. 0 for o and 1 for
i)
Reminder: too many of them come out of a bottle
Use a word or phrase but insert some extra
characters
password [a far too obvious choice!] becomes
pass!?word
reminder: oh, that password!?
counterwait becomes
counter42!wait
Use a phrase or a sentence that's memorable (and that you can type
quickly)
I'm an Eagles fan for life
reminder: what I said when
I was 10
Use two or three unrelated words, separated by numbers or special characters
| Hence bad11cow99song
Or maybe just the words, even without the separators? [The cartoon's a bit techie, but feel free to click on it: | 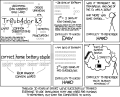 |
Use an acronym, e.g. the first letters of a phrase or sentence
that's memorable to you
'I'm an Eagles fan for life' becomes
IaEffl
reminder: what I said when I was 10, quickly
But this needs to be
lengthened, maybe with a number and an extra word
Hence perhaps
IaEffl77fan
Use a combination of special characters, e.g. by choosing the
ones at the top of the keyboard that are above the letters that make up a
memorable word
e.g. QWERTY becomes !@#$%^
[This just shows the idea.
Those keys are in sequence, so it fails the obviousness test. And, for the
same reason, don't use 'smileys' like (:-) ]
Many sites that offer advice on password creation include suggestions that are impractical (along the lines of 'make sure your passwords are so complicated that you can't possibly remember them'). But here are a couple of documents that are worth reading:
A short version of current thinking is at the top of this page.
Sites like passwordmeter.com, testyourpassword.com and howsecureismypassword.net may be genuinely helpful, but on the other hand they might be trying to capture your passwords.
Avoid keying your password into such sites. But you could try out possible passwords that have a similar general shape to your password.
Alternatively, you may prefer to rely on a 'brandname' web-site. I found no such tools at consumer-friendly sites such as EFF, EFA, EPIC, Privacy Rights, APF or Privacy International, but these two came to hand:
This document has focussed on what people can do to protect their own passwords. But service-providers also have important roles to play. Things that they should do include:
If you're not sure about which of these your service-provider does, look at the on-line documentation (often called 'FAQs' - Frequently Asked Questions), and if that doesn't answer your questions, email them and ask.
If a service-provider doesn't do these things, you should seriously consider complaining to them, or changing to another service-provider.
Passwords are a form of 'authenticator'. That's a general word for some kind of evidence to support an assertion. In this case, the assertion a person makes when they try to login is that they're the appropriate person to use that account.
Some alternative authenticators exist, including:
All of these have strengths, and all of them have weaknesses as well.
For example, digital signature technologies have theoretical appeal, but also multiple vulnerabilities. (Among other things, the use of the signing key may be protected by a password, which represents the weakest link in that particular security chain).
Biometrics, contrary to the nonsense put about by marketers, are highly vulnerable as well, in particular because a biometric is not a secret, can be easily captured and replayed, in some cases is spoofable (i.e. the device can be tricked into accepting something it shouldn't), and is irrevocable (e.g. you have only one right thumb, and it has a single unique print-pattern; so when someone acquires a copy of that thumbprint, it's compromised and can never be reliably used again).
The most effective approach is 'multi-factor authentication', i.e. using two or more authenticators that are unrelated to one another. Banks are increasingly using what you know (a password) combined with what you have (an additional, one-time password - which may be generated by a gadget, or sent to the user when it's needed, but via a different channel or path such as a pre-registered device different from the one the password was typed on).
'Factsheet 15 - Understanding password security' Dept of Broadband, Communications and the Digital Economy, 2006, at http://www.staysmartonline.gov.au/__data/assets/pdf_file/0020/19523/F15_password_security.pdf
Wikipedia articles on password, passphrase and password strength
Thanks to several link community-members who provided feedback on the first draft, and to my daughter, who provided a valuable real-world test of it.
Roger Clarke is Principal of Xamax Consultancy Pty Ltd, Canberra. He is also a Visiting Professor in the Cyberspace Law & Policy Centre at the University of N.S.W., and a Visiting Professor in the Research School of Computer Science at the Australian National University.
| Personalia |
Photographs Presentations Videos |
Access Statistics |
 |
The content and infrastructure for these community service pages are provided by Roger Clarke through his consultancy company, Xamax. From the site's beginnings in August 1994 until February 2009, the infrastructure was provided by the Australian National University. During that time, the site accumulated close to 30 million hits. It passed 65 million in early 2021. Sponsored by the Gallery, Bunhybee Grasslands, the extended Clarke Family, Knights of the Spatchcock and their drummer |
Xamax Consultancy Pty Ltd ACN: 002 360 456 78 Sidaway St, Chapman ACT 2611 AUSTRALIA Tel: +61 2 6288 6916 |
Created: 23 July 2011 - Last Amended: 1 September 2017 by Roger Clarke - Site Last Verified: 15 February 2009
This document is at www.rogerclarke.com/II/Passwords.html
Mail to Webmaster - © Xamax Consultancy Pty Ltd, 1995-2022 - Privacy Policy